Project URL: https://github.com/sleventyeleven/Kubernetes-Harvester
What is Kubernetes Harvester?
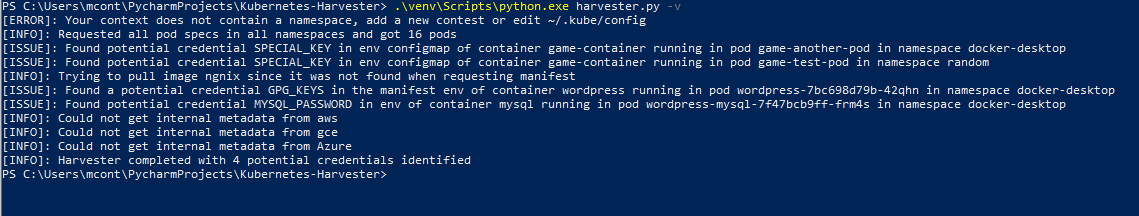
Harvester is a new python based project that attempts to leverage access in order to gather potentially sensitive information. Its designed to either leverage the access of users credentials or the default access granted to a pod via automountServiceAccountToken, which I wrote about recently. The harvester.py script currently primarily targets pod container environment variables, container manifest environment variables, and config map entries utilized as environment variables, to look for potential credentials.
Why Create A Credential Harvester
The default admission controls in many of the Kubernetes implementation apply a read/view policy to newly created users. However custom policies, admissions, and operators have become more common place. What’s more troublesome is the read permissions given to the automountServiceAccountToken by default. Without adjusting or disabling service tokens, compromised containers could effectively read all pod specs in all namespaces. With access to all pod specs, an attacker could potentially gather credentials or other sensitive information. Harvester is a tool that attempts to help automate the review process.
How Kubernetes Harvester Works
The harvester.py script utilizes the automountServiceAccountToken mounted within a given container or the standard user credentials within the Kube config file (~/.kube/config). Then the Kube API server is queried to look for sensitive information within the pod spec of each pod in the following steps.
- Use access to request pod specs for all namespaces within the cluster.
- Parse all pod specs to map and dedupe container container information
- Review each containers environment variables for sensitive values
- Review each config map entry, mapped to container environment variables for sensitive values
- Attempt to pull each container image and review the manifest environment variables for sensitive values
- Attempt to request authentication tokens from the internal metadata API for each of the major cloud provider
Other Resources:
- Introduction to Kubernetes – A Free introduction course diving into Kubernetes as a tool for containerized infrastructure. Its a a great place to begin if your just getting started with Kubernetes.
- The Linux Foundations Official Course – This is the most robust general knowledge based course I’ve seen. If you want to learn Kubernetes and how to do almost anything with it, get the CKA + CKAD combo package.