Although I wont cover all of the team challenges that Kernel Panic completed during the NCL 2014 Team Post Season round, several stood out amongst the rest.
I’d also note, some of the challenges from the individual round were covered on the site of my Cyber Defense Team.
Passwords 1:
For this challenge, we were given a password hashing algorithm written in java script. I heard from some other teams, that they had successfully reverse engineered the algorithm; in order to decode the passwords. However, we had s better rate of success just running a word list through the algorithm and doing some string comparison. In the end it turned out, that the passwords were all World of Warcraft towns, and a few Google’s made a winning word list.
Recon 2:
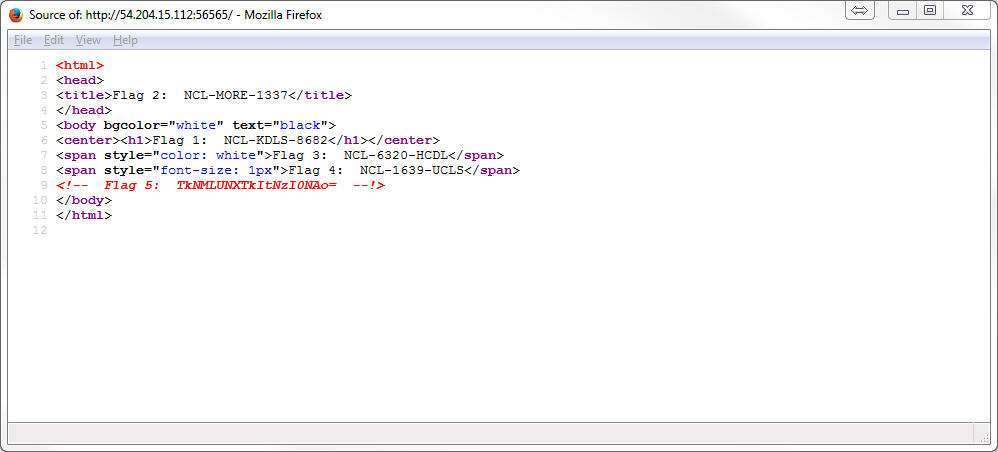
In this challenge we were asked to find the port on a server that was actually running an HTTP 1.0 compatible server and to then to find several flags. After a very confusing start, we discovered that the server was running port spoof. This nifty piece of software, randomly generates one of roughly 400 legitimate service banners, on each of the unused ports. Several of these possible banners being Apache products. However, it turned out that the web server was running nginx, which only really has one service banner. So we were able to use nmap to request the service banner for each port and then grep through the results for nginx. We then found the correct port to be 56565, and the first 5 flags could be found from viewing the pages source.
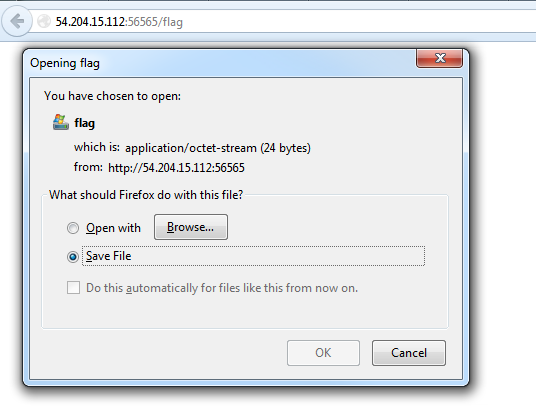
In order to get the last flag, you would have had to guess or know from previous exercise (<- what the heck NCL), that you can just throw a /flag on the end of the site URL. You will then be served a text file with the flag information inside it.
Web 3:
Using the CHANGELOG.txt file of the site, we were quickly able to identify that the server was vulnerable to a string of Drupal vulnerabilities that had recently surfaced. However, due to the destructive (<- no fun NCL) nature of these SQL based exploits, we were unable to gain a strong foot hold within this box. It should be noted that towards the end of the session a metasploit module (drupal_drupageddon) was even release to exploit this vulnerability, and still very few teams were able to capture the flag.
Exploit 3:
This challenge was all about gaining access to the system and gathering flags. The exploit being the shellshock vulnerability allowing for a special string of characters to be passed into a web function that processes bash commands. In this case, the vulnerability existed in a php-cgi script called dpkglist. This allowed for a specially encoded string to be passed as the user agent of an http request, to the effected web server. This string can also be manipulated to allow for fully qualified commands to be entered and their output to be displayed, if they output only one stream. Bellow is the curl command I engineered during the challenge to run the cat command on the flag files.
curl -H “User-Agent: () { ignored; }; echo Content-Type: text/plain ; echo ; echo ; /bin/cat flag.cgi;” -k https://54.83.28.186/cgi-bin/dpkglist.cgi
Special thanks to the other members of my team:
Turner “Shadow_Crux” England
Wade “HelpdeskMan” Schimmoeller
Elliot “CiscoMan” Stidd
Michael “Seleventyeleven” Contino